Forensic Evidence (Faraday) Bags-Keeping Electronic Evidence Secure inside a Faraday Cage
We are all aware of the proliferation of electronic devices that we use in our daily lives, in fact, most of us have several electronic devices that we use regularly. These devices can be our cell phones, which have essentially become miniature computers that keep track of our appointments, finances, email, phone calls, and text messages. Additionally, we have our computers, tablets, and PDA’s. All of these devices help us to keep our lives in order by making our information available to us at all times.
When a person is arrested or suspected in crime, often a search warrant is issued for vehicles, the home, and often includes the seizure of digital devices, as these devices hold a lot of information about the suspect. The telephone can provide a detailed GPS map of where the phone has been and at what time, along with communication, contact information, and contacts. The computers often keep detailed records of financial transactions, in some cases evidence of child pornography or molestation.
Why use a Forensic Bag For Electronic Evidence?
These devices can be often be accessed in a number of ways wirelessly; one of the reasons that the owner of the device might try to access the device once it has been seized by law enforcement is to destroy, alter, or remove incriminating records from the device. It is the responsibility of the investigators to protect the integrity of this digital information and device while the device is in their custody for evaluation.
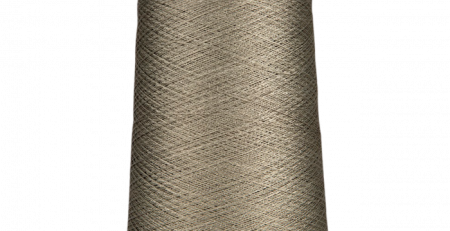
All ways of accessing these devices involve the wireless access through an electromagnetic field. In order to protect the device from being accessed remotely, the device is placed in an electronic evidence pouch, which is a pouch fabricated of metalized textiles. This evidence pouch acts as a Faraday Cage, preventing the penetration of the pouch by electromagnetic fields, named after Michael Faraday, who first noted this effect in 1836.
The investigators transport these devices to their computer labs secure in the confines of these Forensic Evidence Bags for analysis and digital evidence collection. These bags are sealable and contain a list of people who secured the bag from time of seizure until the evidence is safely stored. This information on this list is called the “Chain of Custody” of the evidence which indicates the sequence of custody, control, transfer, analysis, and disposition of the materials required by law to prove that the evidence wasn’t tampered with while in custody of the legal system.
Note: These electronic evidence pouches and Faraday Bags aren’t just used for custody of evidence, they allow safe storage of individual electronic devices in your home or while you travel, allowing you peace of mind in knowing that they can’t be accessed, hacked, or altered while they are safely protected “in the bag”. Please call us to find out about these excellent security products can help you in your private life!
V Technical Textiles, Inc.
www.vtechtextiles.com
info@vtechtextiles.com
(315)-597-1674 PHONE
(315)-597-6687 FAX













Leave a Reply